For R&D and Regulatory managers, the standardization landscape is evolving. While EN18031 has been the foundational standard under RED for CE marking, the EU is now transitioning to a new “Horizontal” series of standards specifically designed for the Cyber Resilience Act (CRA).
EU Cyber Resilience Act (CRA) transforms cybersecurity from a “best practice” into a legal requirement for the entire lifecycle of a Product with Digital Elements (PwDE). This shift requires a move away from just technical controls toward comprehensive organizational activities.
Under CRA, liability for non-compliance can reach up to €15 million or 2.5% of global turnover. For a Regulatory Manager.
To maintain the legal right to use the CE mark, manufacturers must now prove their products are designed, produced, tested and even disposed of with an appropriate level of security based on documented risks.
- Core Principles of the CRA Framework
The regulation is built on four fundamental pillars that must be integrated into your company’s DNA:
- Risk-Based Approach: Every technical file needs to include a documented cybersecurity risk assessment for all design decisions.
- Security by Design: Vulnerabilities must be addressed during the development phase, ensuring products are launched without known exploitable flaws.
- Security by Default: Products must be delivered in their most secure configuration.
- Transparency: Manufacturers must provide clear documentation on support periods and how users can securely manage their devices.
- The Mandatory SBOM: You Can’t Secure What You Don’t Know
A critical new requirement is the Software Bill of Materials (SBOM).
- What it is: A machine-readable inventory of all software components, including 3rd-party and open-source libraries.
- Why it’s vital: The SBOM must be continuously mapped against vulnerability databases (like CVE) to ensure your supply chain remains secure.
- Management: Manufacturers are now legally responsible for the security of every component they “buy in” from sub-contractors.
- Understanding Product Risk Categories
Compliance depth is determined by how your product is classified:
- Default Category (90% of Market): Includes items like smart home devices or simple consumer apps. These typically allow for Self-Assessment or an accredited lab (Module A), though a full technical file is still required.
- Important Products (Class I & II): Includes browsers, password managers (Class I), and firewalls or smart meters (Class II). Class II products always require a Notified Body
- Critical Products: Reserved for high-assurance items like hardware security modules (HSMs) and smart cards, requiring the highest level of certification.
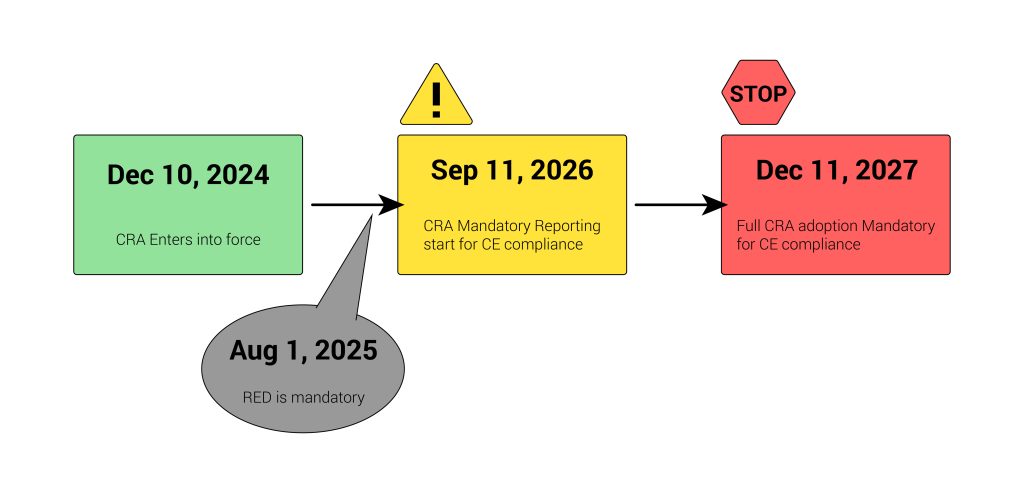
- Critical Operational Milestones
To maintain market access and the legal right to affix the CE mark, mark your calendars for these two non-negotiable deadlines to keep your products on the EU market:
- September 11, 2026 – Reporting Obligations Kick In:
The “Grace Period” for incident reporting ends here.
- The Mandate: You must report actively exploited vulnerabilities to ENISA within 24 hours.
- The Standard: Align your processes with the new EN40000-1-3 standard and to meet the 24 hours window.
- This applies to all products currently on the market, not just new ones.
- December 11, 2027 – Full Enforcement:
This is the “Hard Cut-off.”
- The Mandate: No product with digital elements can be sold in the EU without demonstrating CRA compliance.
- The CE Requirement: Compliance with the EN40000 series (and where applicable, EN18031) becomes the legal basis for the Declaration of Conformity. Without this, the CE mark is invalid for the EU market.
- The CRA becomes fully applicable across the board.
- Compliance with harmonized standards (the EN40000 series) becomes the mandatory path for affixing the CE mark.
- Practical Roadmap for Managers
The transition from EN18031 to EN40000 is a “delta” (a set of additions), not a total restart. If you were already tested against EN 18031, you made big progress.
- Audit your portfolio: Classify your existing and upcoming PwDEs immediately.
- Map the Delta: Review EN 40000-1-4 against your current EN 18031-1/2/3 technical files to identify new security controls required by the CRA.
- Audit your Supply Chain: The CRA requires a Software Bill of Materials (SBOM). Start requiring these from your vendors now so you aren’t stuck in 2027.
- Engage an Accredited Lab Early: Early testing in an ISO 17025 accredited lab ensures your technical documentation can withstand your customer’s needs and a regulatory audit.
- Implement a CVD Policy: Establish a Coordinated Vulnerability Disclosure policy to receive security info from external researchers.
- Update your QMS: Ensure your Quality Management System includes processes for vulnerability handling and mandatory reporting.
The bottom line: By treating the CRA as a strategic roadmap rather than a hurdle, you ensure that your products are not only compliant but resilient for the long term.
Don’t let the 2026 reporting deadlines catch you off guard. Integrating risk-based approach, Security by Design, testing and vulnerability handling into your PwDE takes time. Start your transition to the CRA requirements today to ensure uninterrupted market access.
Contact our ISO 17025 accredited laboratory today to schedule a roadmap consultation.
For transparency, the writer is in the EU CENELEC JTC13 expert team which defines these new standards.